The phrase How Darknet Vendors Work often triggers curiosity, confusion, and misinformation. Popular media tends to sensationalize darknet markets, yet the reality is more structured—and more complex—than headlines suggest.
Darknet vendors operate within anonymous marketplaces hosted on privacy-focused networks like Tor. However, they do not function like typical eCommerce sellers. Instead, they work within encrypted ecosystems shaped by trust systems, reputation metrics, and constant law enforcement pressure.
This guide explains how darknet vendors operate structurally, what systems support them, and why new users should understand the risks before exploring these environments.
Understanding the Marketplace Environment
Before explaining How Darknet Vendors Work, it’s important to understand the infrastructure around them.
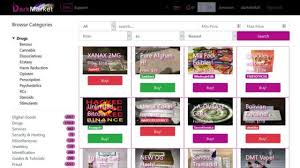
Darknet vendors typically list products on hidden services accessible through Tor. These marketplaces resemble standard online stores in design. Nevertheless, they differ significantly in governance and risk exposure.
Most marketplaces include:
- Vendor registration and verification systems
- Escrow-based payment mechanisms
- Reputation and feedback scoring
- Moderation teams
- Dispute resolution systems
However, unlike surface web platforms, these systems operate without legal consumer protection.
For readers unfamiliar with hidden services and indexing behavior, our guide to
Dark Web Search Engines Explained
offers helpful background on how these environments remain partially visible.
Marketplace Structure and Vendor Registration
At a structural level, vendors cannot simply list products anonymously without process. Most markets require registration and sometimes a bond or deposit.
Typically, vendors must:
- Create a PGP key for encrypted communication
- Agree to marketplace rules
- Build a reputation through successful transactions
- Maintain operational security practices
Because anonymity is central, communication often occurs through encrypted messaging within the platform. However, operational mistakes frequently expose users.
According to reporting by Europol, operational security failures remain one of the most common factors leading to arrests in darknet investigations.
Therefore, marketplaces attempt to create structured environments. Yet, they cannot eliminate risk.
How Darknet Vendors Work Inside Escrow Systems
To understand How Darknet Vendors Work, escrow is a key concept.
Escrow systems temporarily hold funds until buyers confirm receipt. This model aims to reduce fraud and create trust between anonymous parties.
Here’s how it generally works at a high level:
- Buyer places an order.
- Funds are locked in escrow.
- Vendor ships product.
- Buyer confirms delivery.
- Funds release to vendor.
However, escrow abuse and “exit scams” remain common. When marketplaces shut down suddenly, vendors and buyers often lose funds.
This is one reason why markets frequently disappear or rebrand. Our breakdown of
Active Darkweb Markets
explains how market instability affects vendors and users alike.
Reputation, Feedback, and Trust Signals
Because vendors operate anonymously, reputation replaces identity.
Marketplace profiles often display:
- Feedback scores
- Sales counts
- Vendor longevity
- Dispute history
Over time, successful vendors accumulate positive reviews, which increases trust. However, fake reviews and manipulation also occur.
Consequently, users must evaluate patterns rather than single comments.
Security researchers frequently warn that reputation systems can create a false sense of safety. As explained by the Electronic Frontier Foundation, anonymity tools protect privacy—but they do not guarantee trustworthiness.
Product Listings and Operational Practices
While product types vary, vendors typically structure listings similarly to traditional eCommerce platforms.
Listings often include:
- Product description
- Pricing tiers
- Shipping region
- Delivery time estimates
- Refund policy
However, because there is no legal recourse, policy enforcement depends entirely on platform moderators.
Importantly, vendor survival depends on consistency. Poor communication, delayed shipping, or unresolved disputes damage reputation quickly.
Security Practices and Anonymity
Another critical aspect of How Darknet Vendors Work involves operational security, often referred to as “OpSec.”
Vendors typically use:
- Encrypted messaging (PGP)
- Anonymous cryptocurrency wallets
- Privacy-focused browsers
- Compartmentalized digital identities
Even so, law enforcement agencies have repeatedly infiltrated and dismantled markets. Investigations often rely on small mistakes, reused usernames, or metadata leaks.
The Tor Project explains that onion services protect network-level anonymity. However, user behavior ultimately determines exposure risk.
In other words, technology can reduce traceability—but it cannot eliminate human error.
Risks for New Users
New users often underestimate the layered risks in darknet environments.
Common risks include:
- Fraudulent vendors
- Marketplace exit scams
- Phishing mirror sites
- Law enforcement monitoring
- Data leaks
- Seized shipments
For example, phishing remains a persistent threat. Fake mirror links frequently appear in forums and directories.
To better understand how link integrity affects security, read our guide on
Dark Web Link Verification
Verification practices reduce—but do not remove—risk exposure.
Legal and Ethical Implications
It is also critical to understand that participating in many darknet marketplaces involves legal risk.
While not all darknet activity is illegal, many markets facilitate prohibited goods. As a result, law enforcement agencies worldwide actively monitor these ecosystems.
According to reporting by BleepingComputer, major darknet marketplace takedowns frequently involve international cooperation and long-term undercover operations.
Therefore, new users should approach darknet research cautiously and lawfully.
Market Evolution and Vendor Adaptation
Over time, vendor strategies have evolved.
Markets shut down. Vendors migrate. Reputation resets. Trust must rebuild.
This cycle mirrors the broader
Darkweb Market Evolution
Vendors who survive long-term typically adapt quickly to:
- Marketplace closures
- Cryptocurrency volatility
- Increased law enforcement pressure
- Escrow system changes
However, long-term stability remains rare.
FAQs About Darknet Vendors
Are all darknet vendors criminals?
Not necessarily. However, many marketplaces host illegal goods. Therefore, legality depends on the specific activity.
Do escrow systems guarantee safety?
No. Escrow reduces fraud risk but does not eliminate exit scams or law enforcement intervention.
Why do vendors disappear suddenly?
Common reasons include marketplace shutdowns, arrests, voluntary exits, or scams.
Can reputation scores be trusted?
They offer signals, but manipulation occurs. Users must analyze patterns over time.
The Broader Context of Anonymous Commerce
When analyzing How Darknet Vendors Work, it helps to zoom out.
Anonymous commerce exists because privacy-focused networks enable pseudonymous interaction. While this can protect journalists and whistleblowers, it can also shield illicit trade.
The technology itself is neutral. Its usage determines consequences.
Therefore, educational understanding is critical.
Conclusion: How Darknet Vendors Work
Understanding How Darknet Vendors Work requires looking beyond headlines. Vendors operate within structured marketplaces built on anonymity, escrow systems, and reputation metrics.
However, these systems remain fragile. Law enforcement pressure, scams, and operational errors constantly reshape the ecosystem.
For new users, the most important lesson is caution. Darknet marketplaces may resemble traditional eCommerce platforms, yet they operate without consumer protections and within significant legal risk.
Education reduces misinformation—but it does not remove danger.