Introduction
Dark web tracking methods are more advanced than many users realize. While anonymity tools like Tor are designed to protect identity, law enforcement agencies have developed techniques to monitor activity and identify patterns across hidden networks.
As a result, the idea of complete anonymity is often misunderstood. Although privacy tools reduce exposure, they do not eliminate all risks.
Understanding how tracking works is essential—not only for cybersecurity professionals, but also for researchers and users who want a realistic view of online privacy.
What Are Dark Web Tracking Methods?
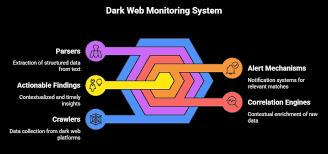
Dark web tracking methods refer to the techniques used by investigators to monitor, analyze, and sometimes identify activity within anonymous networks.
Unlike traditional tracking, these methods do not rely on simple IP logging. Instead, they focus on behavior, patterns, and operational mistakes.
Common approaches include:
- Traffic correlation analysis
- Metadata tracking
- Behavioral fingerprinting
- Financial tracing
Because of this, tracking often depends more on patterns than direct identification.
How Dark Web Tracking Methods Work
To understand how tracking happens, it is important to look at the systems behind anonymous browsing.
Traffic Analysis and Correlation
One of the most widely used techniques is traffic analysis. Instead of breaking encryption, investigators analyze the timing and volume of data entering and leaving the network.
By comparing patterns, they can identify potential connections between users and destinations.
Even though Tor encrypts traffic, correlation attacks can still reveal relationships under certain conditions.
👉 To better understand how hidden services operate, see:
how onion search engines index hidden services
Metadata Collection
While content may be encrypted, metadata often remains accessible. This includes information such as:
- Connection times
- Data size
- Frequency of activity
Over time, these details can reveal behavioral patterns.
Endpoint Vulnerabilities
Tracking does not always target the network itself. Instead, investigators may focus on endpoints, such as user devices or servers.
For example:
- Malware can expose identity
- Misconfigured browsers may leak data
- Outdated systems can be exploited
As a result, technical weaknesses often play a major role in tracking.
Behavioral Tracking and Pattern Analysis
User Behavior Patterns
Even in anonymous environments, users tend to repeat behaviors. These patterns can be used to build profiles.
Examples include:
- Writing style
- Login timing
- Navigation habits
Over time, these behaviors can become identifiable.
Account and Identity Reuse
Reusing usernames or credentials across platforms is a common mistake. Investigators can link accounts based on these overlaps.
👉 To understand how trust and identity work in these environments, see:
how darknet vendors build trust and reputation
Financial Tracking Methods
Cryptocurrency Analysis
Cryptocurrency is often seen as anonymous, but most transactions are recorded on public blockchains.
Investigators use blockchain analysis tools to trace:
- Transaction flows
- Wallet connections
- Spending patterns
👉 For a deeper understanding, read: dark web cryptocurrency payments explained
Escrow and Marketplace Monitoring
Marketplaces often act as central points for transactions. Law enforcement can monitor these platforms or even infiltrate them.
Tracking may involve:
- Observing escrow systems
- Monitoring vendor activity
- Analyzing transaction timing
👉 To explore how these systems work, see: darknet market escrow explained
Infrastructure-Level Tracking
Server Seizures and Network Control
In some cases, authorities gain access to servers hosting hidden services. This allows them to collect data directly.
Operations may involve:
- Seizing infrastructure
- Running controlled nodes
- Monitoring traffic flows
Organizations like Europol frequently coordinate such efforts.
🔗 For authoritative reference, visit:
Europol cybercrime operations
Malicious or Controlled Nodes
Another method involves operating nodes within the network. By controlling entry or exit points, investigators can gather useful data.
Although encryption remains intact, traffic patterns can still be analyzed.
Limitations of Dark Web Tracking Methods
Despite these techniques, tracking is not always successful.
Strong Encryption Barriers
Encryption still provides a high level of protection. Breaking it directly is extremely difficult.
Instead, most tracking relies on indirect methods.
User Awareness and Best Practices
Users who follow strict privacy practices are harder to track. Avoiding mistakes significantly reduces exposure.
Resource Limitations
Tracking requires time, expertise, and coordination. Not all activity is monitored equally.
How Users Can Reduce Tracking Exposure
While tracking methods are advanced, users can take steps to improve privacy.
Start by minimizing identifiable behavior and avoiding unnecessary interactions.
Additional practices include:
- Using updated software
- Avoiding credential reuse
- Limiting personal data exposure
- Verifying links before access
👉 To explore safe navigation practices, see: how to find onion sites safely
The Role of Privacy Research and Advocacy
Privacy organizations continue to study tracking risks and develop countermeasures.
The Electronic Frontier Foundation emphasizes the importance of transparency and user education.
🔗 For first class reference, see: EFF privacy research and surveillance insights
Evolving Trends in Tracking and Surveillance
Increasing Use of Data Analysis
Modern tracking relies heavily on data analysis rather than direct surveillance.
Cross-Platform Correlation
Activity is often tracked across multiple platforms, not just the dark web.
Expanding Cybercrime Monitoring
Security platforms like BleepingComputer frequently report on new tracking techniques and vulnerabilities.
🔗 For reference, checkout:
latest cybersecurity threat reporting
FAQs: Dark Web Tracking Methods
Can law enforcement track dark web users?
Yes, but not always directly. Tracking usually depends on patterns, mistakes, or external data.
Is Tor completely anonymous?
No. While it provides strong privacy, it does not guarantee full anonymity.
What is the most common tracking method?
Traffic analysis and behavioral tracking are among the most common.
Can cryptocurrency be traced?
Yes. Blockchain analysis allows investigators to follow transaction patterns.
How can users stay safer?
By combining tools with careful behavior and awareness.
Conclusion: Dark Web Tracking Methods
Understanding dark web tracking methods provides a more realistic view of online anonymity. While privacy tools offer strong protection, they are not foolproof.
Ultimately, tracking often relies on patterns, behavior, and technical weaknesses rather than direct identification. By staying informed and adopting better practices, users can significantly reduce their exposure.